Credit: Colin / Wikimedia Commons, via Wikimedia Commons
You’ve come to this post thinking that hacking into Wi-Fi networks is easy right?
Well, not necessarily, unless the Wi-Fi password is one of these passwords.
You see, whenever you boot up your laptop out at home, or somewhere close to a Wi-Fi network, you’ll notice that there’s a little lock next to the network name (also known as the SSID, or Service Set Identifier).
What this means is that there is some security behind the Wi-Fi network to stop hackers from compromising the network.
In general, there are two types of Wi-Fi security:
Wired Equivalent Privacy (WEP)
Wired Equivalent Privacy (WEP) is the most widely used Wi-Fi security algorithm in the world.
The reason it is the most widely used is due to age, backwards compatibility, and the fact that it appears first in the encryption type selection menus in many router control panels.
Even though WEP uses 128 bit and 256-bit encryption, the system is highly vulnerable and systems that rely on WEP should be upgraded or, if security upgrades are not an option, replaced.
Wi-Fi Protected Access (WPA)
Wi-Fi Protected Access was the Wi-Fi Alliance’s direct response and replacement to the increasingly apparent vulnerabilities of the WEP standard.
It was first used in 2003 and uses a 256-bit encryption model which is tough to hack compared to the 64-bit and 128-bit keys used in the WEP system.
WAP2 is an updated version of WPA and was introduced in 2006.
One of the most significant updates between WPA and WPA2 is the fact that WPA2 uses AES algorithms and has also seen the introduction of CCMP (Counter Cipher Mode with Block Chaining Message Authentication Code Protocol).
There was a security vulnerability in WPA2 but it does require attackers to essentially chain four vulnerabilities together and many wireless access point manufacturers already have updates available to patch or mitigate the vulnerabilities.
You can read more about the Key Reinstallation Attacks vulnerability here.
So, as you can see, hacking into a Wi-Fi device is not at all easy and without a password, you’re not going to get access to that network – period.
If do however fancy finding vulnerabilities in WPA2 yourself and think you can prove me wrong, then I recommend the book below from Amazon to getting started:
If you’re after an easier way to hack Wi-Fi passwords then read on.
This is particularly useful if you have either forgotten the password on your own Wi-Fi network and you can’t be bothered to go to a a café, buy a latte, and use the “free” public Wi-Fi there.
Learn Ethical Hacking From Scratch (Udemy, #CommissionsEarned)
Enter the Windows Command Prompt
This technique only works to recover a Wi-Fi password providing that you have previously connected to the Wi-Fi network on your laptop.
This works because Windows 8 and 10 create a profile of every Wi-Fi network that you have ever connected to.
However, if you tell Windows to forget the network, then the password will also be forgotten and this will never work.
Most people don’t do that in any case.
Please note that this guide is meant for educational purposes only and you should try this with your own Wi-Fi network only (or a friends network if you have their explicit permission).
It is however a great way to find out the password to your own Wi-Fi network if you can’t remember it due to its length or complexity.
There is one more caveat and this is this requires you to open a Windows Command Prompt with administrative privileges.
Step 1:
To do this, use Cortana to search for “cmd” and the menu will show Command Prompt.
Simply, right-click and and select “Run as administrator.”
When you do this, a black box full of white text will appear with the prompt inside.
Basically, it’s the line with a > at the end and probably looks something like C:WINDOWSsystem32>.
Step 2:
You should also see a blinking cursor which basically indicates where you should type.
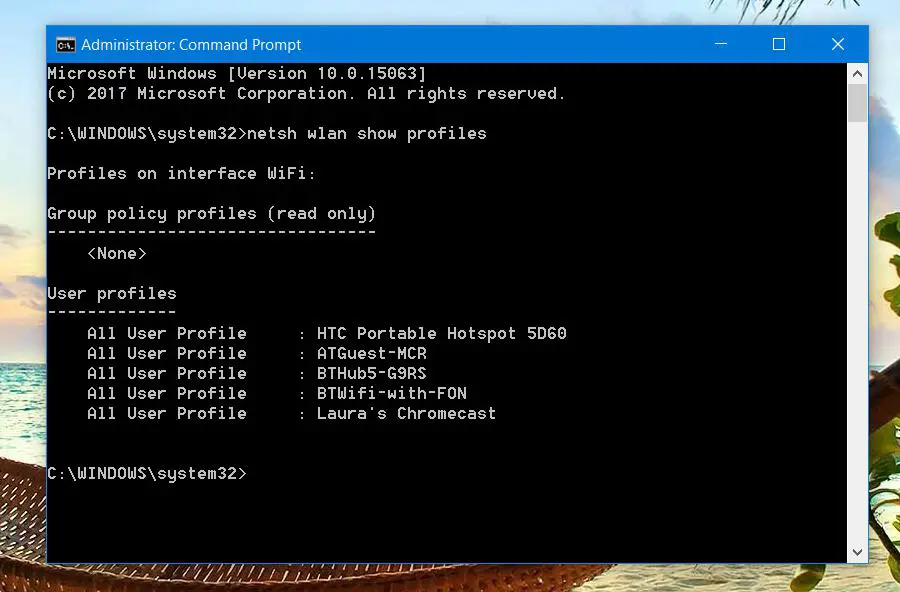
Type: netsh wlan show profiles
The results will basically bring up a section called User Profiles.
There is a User Profile for all the Wi-Fi networks (aka WLANs, or wireless local area networks) you’ve accessed and saved in the past.
Step 3:
From the list above, pick the one you want to get the password for, highlight it, and copy it.
Next, type the following, netsh wlan show profiles (The Name of the Wi-Fi You Selected to Hack) key=clear
Note that if the network name has spaces in it, you will need to include quotation marks around the network name.
In my example, I entered netsh wlan show profiles BTHub5-G9RS key=clear
src=”https://bonkersabouttech.com/wp-content/uploads/2020/01/show-wifi-password-windows-cmd-992017.jpg” alt=”Show WiFi password Windows command prompt (cmd)” width=”894″ height=”591″>In the data that comes up, look for “Security Settings” and next to “Key Content” is the Wi-Fi password. I’ve hidden mine for obvious reasons in the above image 😉
If you happen to use macOS and you’ve gotten this far, then , open up the Spotlight search (Cmd+Space) and type terminal to open up the Mac equivalent of the Windows command prompt.
Type the following, but obviously replace the Xs with the network name.
security find-generic-password -wa XXXX
Resources:
How to Hack A Wireless Network (Amazon, #CommissionsEarned) – Definitive guide to (ethically) hacking wireless networks
Hacking books – A comprehensive guide to the best ethical hacking books